Microchip’s Trust Platform for its CryptoAuthentication family looks to help companies of all sizes to implement secure authentication at a time when the vulnerabilities in the Internet of Things (IoT) have created significant challenges for developers.
Hardware-based security is the only way to protect secret keys from physical attacks and remote extraction, but extensive security expertise, development time and costs are required to configure and provision each device.
Manufacturers typically have only been able to support configuring and provisioning for high-volume orders, leaving companies with low- to mid-sized deployments with low performing options.
Microchip’s Trust Platform addresses this problem and consists of a three-tier offering, providing out-of-the-box pre-provisioned, pre-configured or fully customisable secure elements, allowing developers to choose the platform best suited for their design.
Trust&GO is the first tier and provides zero-touch pre-provisioned secure elements with a Minimum Orderable Quantity (MOQ) as low as 10 units. Device credentials are pre-programmed, shipped and locked inside the ATECC608A for automated cloud or LoRaWAN authentication onboarding. In parallel, corresponding certificates and public keys are delivered in a “manifest” file, which is downloadable via Microchip’s purchasing e-commerce store and distribution partners.
This will save months in development time and significantly simplifies provisioning logistics, making it easy for mass market customers to secure and manage edge devices without the overhead cost of third-party provisioning services or certificate authorities.
For customers who want more customisation, the program includes the TrustFLEX and TrustCUSTOM platforms.
The second tier in the program is TrustFLEX. It enables customers to use the certificate authority of their choice while still benefiting from pre-configured use cases. These use cases include baseline security measures such as Transport Layer Security (TLS) hardened authentication for connecting to any IP-based network using any certificate chain, LoRaWAN authentication, secure boot, Over-the-Air (OTA) updates, IP protection, user data protection and key rotation. This reduces the time and complexity involved in customising the device without the need for customised part numbers.
For customers who want to customise their designs, the third tier in the program – TrustCUSTOM – provides customer-specific configuration capabilities and custom credential provisioning.
“The uptick in successful attacks on software-based security solutions underscores the need for companies to adopt industry best practices, including isolating private keys in secure elements,” said Nuri Dagdeviren, vice president of Microchip’s secure products business unit. “Microchip’s Trust Platform makes hardware-based security simple and cost-effective for companies of all sizes, removing the barriers associated with configuring and provisioning devices.”
Microchip has worked with Amazon Web Services (AWS) to enable a simplified onboarding process into AWS IoT services for products designed with all variants of the Microchip Trust Platform.
The ATECC608A provides Common Criteria Joint Interpretation Library (JIL) “high”-rated secure key storage and hardware-based root of trust storage and cryptographic countermeasures. Consequently, the device is protected against most known physical attacks.
Microchip’s secure manufacturing facilities safely provision keys, ensuring that keys are never exposed to any party during provisioning or the lifetime of the device.
The ATECC608A can be paired with any microcontroller and microprocessor and engineers can use the Trust Platform Design Suite, which includes:
- A guided “use case tool”
- Executable Python tutorials running on Jupyter notebooks
- C code examples for each use case
- A “secret exchange” utility
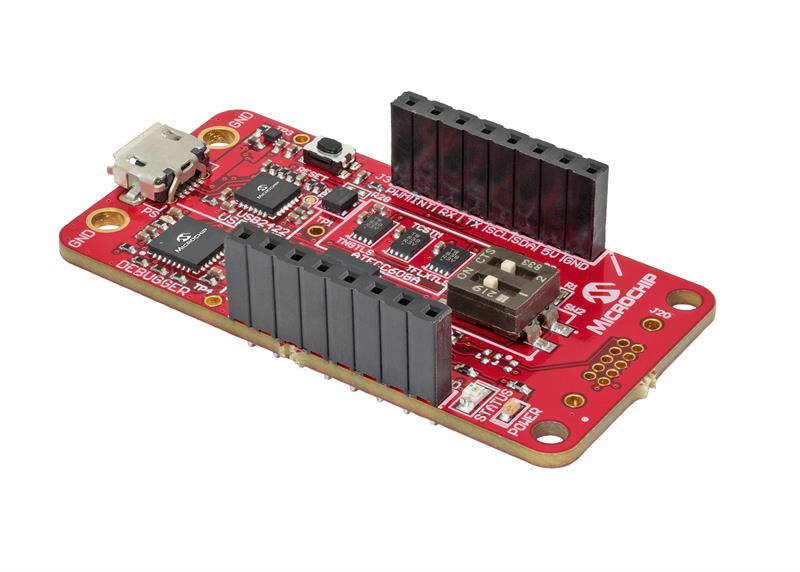
- The Trust Platform hardware development kits













